You connect your wallet to what looks like a legitimate platform. You approve a routine permission request and within minutes, everything is gone. No second prompt, confirmation, or way back.
That is how wallet draining works.
What is happening
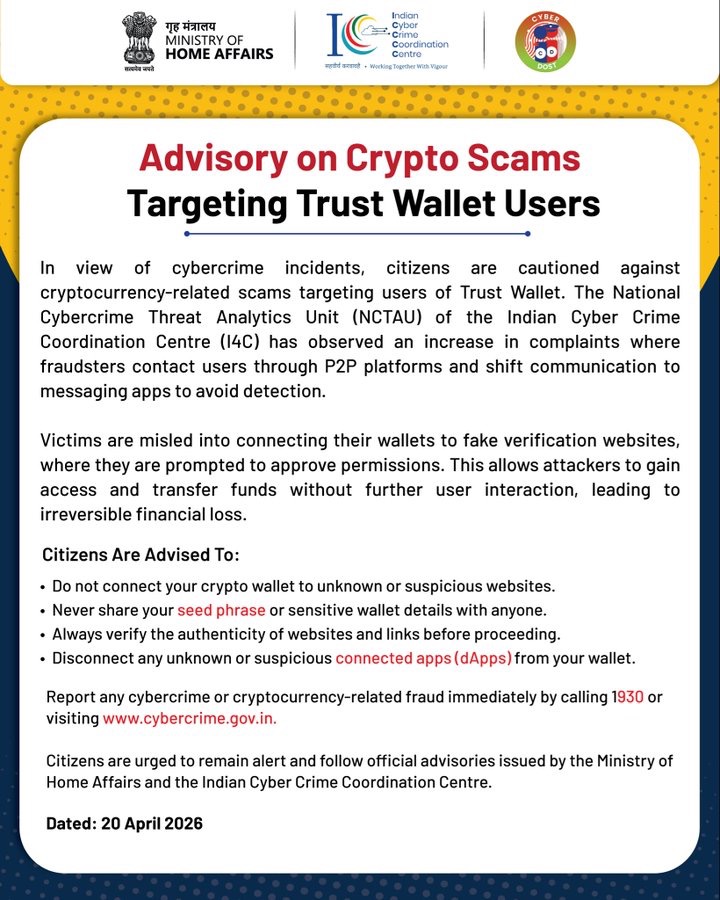
India’s National Cybercrime Threat Analytics Unit (NCTAU), the analytical wing of the Indian Cyber Crime Coordination Centre (I4C) under the ministry of home affairs, issued an Advisory on April 20, 2026, following a significant rise in complaints of cryptocurrency fraud targeting Trust Wallet users.
Contact usually starts on a peer-to-peer (P2P) trading platform. A fraudster poses as a buyer or seller, then shifts the conversation to WhatsApp or Telegram to stay out of the platform’s view.
Once off-platform, the victim is told their wallet needs verification before the transaction can go through. Next, the victim receives a fake website link that looks like a blockchain verification service. Connecting a wallet to that site triggers a hidden smart contract permission. The drainer script then executes automatically, moving funds with no further input from the victim. The loss is immediate and cannot be reversed.
Why it works
Crypto wallets work on a permission model. When you connect to a decentralised application (dApp) or website, you approve certain access rights. Those approvals let dApps interact with your tokens, but unlimited or lingering permissions leave a wallet open to abuse.
Wallet drainers do not hack blockchains. They abuse legitimate token functions. The moment a victim signs a malicious contract, it has authorisation to move assets out of the wallet. Many people lose everything within seconds.
The off-platform shift is deliberate. P2P marketplaces have fraud detection; messaging apps do not. And even when Trust Wallet’s own Critical Risk Alert fires, a two-screen warning that requires the user to explicitly acknowledge the risk before proceeding, scammers often talk victims through clicking past it.
Why recovery is difficult
There is no ombudsman for crypto fraud in India, no compensation scheme, and no regulator you can escalate a wallet draining complaint to beyond the cybercrime portal. Crypto assets are not regulated as financial instruments: they are taxed as virtual digital assets under the Finance Act 2022, and exchanges are required to register with the Financial Intelligence Unit (FIU-IND) under the Prevention of Money Laundering Act, but there is no statutory protection for individual holders if an exchange collapses or a wallet is drained.
The legal complaint route exists but is narrow. A wallet draining case would likely be registered under the Bharatiya Nyaya Sanhita (cheating and dishonest inducement) and Sections 66C and 66D of the IT Act (identity theft and cheating by impersonation). The problem is that the victim technically approved the transaction. From a purely technical standpoint, no unauthorised access occurred the user signed the contract. That ambiguity affects which investigative tools apply and how quickly law enforcement can act.
The most realistic path to any recovery is the PMLA route. If the scammer cashed out through a FIU-registered exchange, there is a transaction trail. FIU-IND can freeze accounts and share data with law enforcement through the Sahyog portal, which I4C has built specifically for crypto investigations. As of March 2025, 49 exchanges were registered with FIU as reporting entities. But this only helps if the fraudster used one of them to convert the funds which sophisticated scammers avoid.
Blockchain transactions are irreversible by design. Unlike bank fraud, where RBI rules require banks to provisionally credit disputed amounts while an investigation runs, no equivalent obligation applies to crypto. Prevention is not just advisable. In most cases, it is the only option.
What you should do
The I4C advisory lists these precautions. They are worth making routine.
• Do not connect your crypto wallet to a link someone sent you. If someone asks you to connect your wallet, that is the red flag.
• Never share your seed phrase. No legitimate platform, support agent, or verification service will ever ask for it.
• Check the URL before connecting. Scam domains often differ from the real thing by a letter or two. If you are not sure, find the official site yourself.
• Audit your connected apps periodically. Trust Wallet lets you see and revoke dApp connections under Settings. Note that disconnecting a dApp does not cancel the token approval, you need to revoke that separately.
If you have already clicked a suspicious link, revoke permissions through your wallet’s connected apps settings straight away. If funds have moved, file a complaint at www.cybercrime.gov.in or call 1930 immediately. The first 48 hours matter; the faster a report is lodged, the better the chances of tracing the transaction before funds are dispersed further.
Wallet draining is one version of a scam structure that runs across almost all crypto fraud. Chainalysis has tracked the growth of crypto drainers closely, and for a period the quarterly value stolen was outpacing even ransomware. The mechanics vary but the script is consistent: unsolicited contact, a move to an unmonitored channel, then a request for access before you have had time to think.
Pausing at any one of those steps usually breaks it. The scam only works when it moves fast.
You can report any cybercrime incidents to the National Cybercrime Helpline by dialling 1930. You can also visit the National Cybercrime Reporting Portal at cybercrime.gov.in to register your complaint online
